Author(s): Rhea Khanna
This paper investigates the utilization of artificial intelligence (AI) techniques for network security and detection of Distributed Denial of Service (DDoS) attacks. It explores the role of AI algorithms, machine learning models, and anomaly detection techniques in enhancing network security, mitigating cyber threats, and improving incident response in the face of DDoS attacks. The paper discusses real-world implementations and case studies showcasing the effectiveness of AI in network security and DDoS attack detection.
Artificial intelligence (AI) has emerged as a transformative force in the domain of network security, offering sophisticated tools and methodologies for tackling complex and evolving threats. Among its many applications, AI has proven particularly effective in addressing Distributed Denial of Service (DDoS) attacks, which are among the most prevalent and disruptive cyber threats facing organizations today.
DDoS attacks involve overwhelming a network, service, -or website with an excessive volume of traffic, rendering it inaccessible to legitimate users and causing significant -operational disruptions. Traditional security measures, while effective to a degree, often struggle to keep pace with the scale and sophistication of modern DDoS attacks. This is where Al technologies come into play, providing advanced capabilities for detecting, analyzing, and mitigating these attacks.
This paper aims to explore the various ways in which AI techniques are applied to network security, focusing on their role in improving the detection and mitigation of DDoS attacks. We will delve into how machine learning models, deep learning frameworks, and anomaly detection algorithms contribute to enhancing network security. By examining these technologies in detail, the paper will highlight their effectiveness, limitations, and the potential they hold for future advancements in cybersecurity.
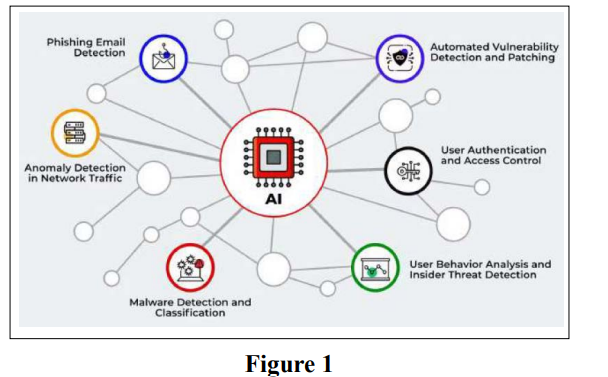
Artificial intelligence encompasses a range of techniques that significantly bolster network security by enhancing threat detection, behavior analysis, and anomaly detection. These techniques include machine learning, deep learning, and natural language processing (NLP), each playing a crucial role in fortifying network defenses and improving incident response mechanisms.
Machine learning, a subset of AI, involves training algorithms to learn from and make predictions or decisions based on data. In network security, machine learning models are employed to identify patterns and anomalies in network traffic that may indicate malicious activities, including DDoS attacks.
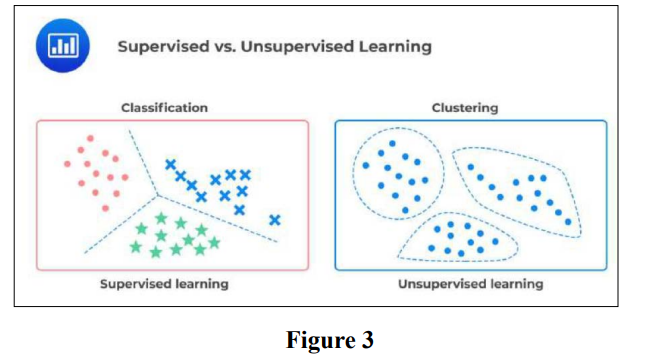
The primary types of machine learning used in network security are supervised learning, unsupervised learning, and reinforcement learning.
Deep learning, a specialized form of machine learning, employs neural networks with multiple layers to process complex data and make highly accurate predictions. In the context of network security, deep learning techniques offer advanced capabilities for threat detection and analysis.
Natural language processing (NLP) involves the interaction between computers and human language, enabling machines to understand, interpret, and generate human language. In net- work security, NLP techniques are used to analyze textual data such as security alerts, incident reports, and threat intelligence feeds.
Overall, the integration of AI techniques into network security frameworks represents a significant advancement in the fight against DDoS attacks and other cyber threats. By lever aging machine learning, deep learning, and NLP, organizations can achieve more accurate detection, faster response times, and enhanced protection against evolving threats. The continued development and refinement of these AI technologies hold the promise of further improving network security and ensuring robust defenses in the face of increasingly sophisticated cyber attacks.
Al algorithms play a crucial role in detecting and mitigating DDoS attacks by analyzing network traffic patterns, identifying malicious activities, and triggering automated responses to mitigate the impact of DDoS attacks on network resources and services. https://www.darkreading.com/cyberattacks-data-breaches/how- ai-ml-can-thwart-ddos-attacks
Machine learning models, including supervised learning, unsupervised learning, and reinforcement learning, are employed for anomaly detection in network traffic. These models learn normal network behavior and can detect deviations indicative of potential DDoS attacks or other cyber threats.
https://www.linkedin.com/pulse/supervised-vs-unsupervised-learning-whats-difference-smriti-saini/
This case study delves into the deployment of an Al-driven Distributed Denial of Service (DDoS) mitigation system within a complex, large-scale network environment. The system in question utilizes advanced machine learning models to detect and neutralize DDoS attacks in real-time, ensuring the continued availability and stability of network services.
The AI-based DDoS mitigation system integrates various machine learning techniques, including supervised and unsupervised learning algorithms, to identify patterns and anomalies in network traffic that are indicative of DDoS attacks. The system continuously monitors incoming traffic, analyzing data in real-time to differentiate between legitimate user requests and malicious traffic. By employing these models, the system can dynamically adapt to evolving attack patterns, thereby enhancing its detection capabilities and reducing response times.
The deployment of this system involved several critical steps. Initially, extensive training data was collected from historical network traffic to train the machine learning models. This data included both normal traffic patterns and known attack signatures. The system was then integrated with existing network infrastructure, utilizing APIs and data streams to receive real-time traffic data. The AI models were calibrated and fine-tuned to ensure accurate detection and minimal impact on legitimate traffic.
The implementation of the AI-based DDoS mitigation sys- tem demonstrated significant improvements in network security. The system effectively detected and mitigated a range of DDoS attack vectors, including volumetric, protocol, and application-layer attacks. Key performance metrics, such as detection accuracy, response time, and system uptime, were evaluated to assess the system's effectiveness. The results highlighted the system's capability to maintain uninterrupted network services while minimizing false positives and minimizing disruption to legitimate users.
This case study explores the practical application of AI- based anomaly detection in network traffic, focusing on how machine learning algorithms are utilized to identify and alert on suspicious activities that may indicate potential security threats, including DDoS attacks.
The AI-powered anomaly detection system employs a variety of machine learning techniques to analyze network traffic patterns. It leverages both statistical methods and advanced algorithms, such as clustering and neural networks, to detect deviations from normal behavior. The system continuously monitors network traffic, applying these algorithms to identify unusual patterns that could signal a potential security threat.
The deployment of the anomaly detection system required the collection of extensive network traffic data for training purposes. This data encompassed typical network activities as well as various attack scenarios. The machine learning models were trained to recognize normal traffic patterns and identify deviations that may signify anomalous behavior. The system was integrated with network monitoring tools to provide real- time alerts and detailed analysis of detected anomalies.
The implementation of the AI-based anomaly detection system resulted in enhanced visibility into network security. The system successfully identified and alerted on a range of suspicious activities, including DDoS attacks and other security threats. Evaluation metrics, such as detection accuracy, false positive rates, and response times, were used to measure the system's performance. The results demonstrated the system's effectiveness in providing timely alerts and facilitating rapid response to potential security incidents.
The paper discusses the various outcomes and benefits derived from leveraging AI technologies for network security and DDoS attack detection. Key advantages include:
Al-driven systems enhance threat visibility by providing detailed insights into network traffic and potential security threats. These systems can analyze vast amounts of data in real-time, identifying patterns and anomalies that may indicate attacks. This increased visibility allows for better-informed security decisions and more effective threat management.
Al technologies enable faster incident response by automating the detection and mitigation of security threats. Real-time analysis and automated alerts facilitate prompt action, reducing the time required to address and neutralize attacks. This rapid response capability is crucial for minimizing the impact of security incidents and maintaining network stability.
Advanced Al algorithms are designed to minimize false positives, ensuring that legitimate traffic is not erroneously flagged as malicious. By leveraging machine learning techniques, these systems can more accurately differentiate between normal and suspicious activities, reducing the occurrence of false alarms and improving overall system efficiency.
Al-driven approaches contribute to enhanced resilience against cyber threats by providing adaptive and scalable security solutions. These systems can continuously learn from new attack patterns and adjust their detection and response strategies accordingly. This adaptability helps organizations stay ahead of evolving threats and maintain robust security postures.
The integration of AI technologies into network security and DDoS attack mitigation strategies offers significant potential for enhancing cybersecurity. Through real-time threat detection, anomaly detection, and automated incident response, Al-driven systems can improve threat visibility, accelerate response times, reduce false positives, and bolster resilience against cyber threats. As organizations continue to adopt and refine AI-based approaches, they can achieve stronger security measures and safeguard critical network infrastructure and services more effectively. The ongoing evolution of AI technologies promises to further advance the capabilities of network security solutions, addressing emerging threats and supporting a more secure digital landscape [1-3].
